 |
Symbols: Object-Orientation, Object Oriented Analysis |
| << Rules for DFD’s: Entity Relationship Diagram |
| Object Oriented Analysis and Design: Object, Classes, Inheritance, Encapsulation, Polymorphism >> |
VU
Information
System (CS507)
LESSON
26
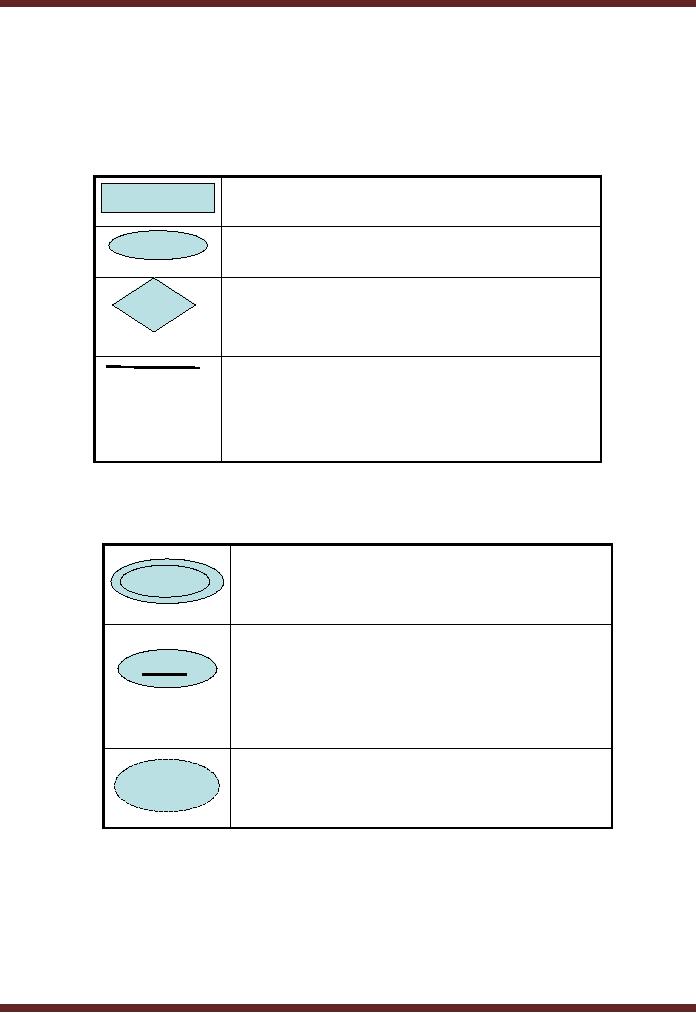
Symbols
Entity
Relationship Diagram as a technical tool
also has predefined set of
symbols. The purpose behind
all
this is to
have standardization in the use of
technique in varied situations. Some major
symbols
commonly
used are as under.
Entity
(a
real world object)
Attributes
(of an
entity)
Relationship
(between
two entities)
Lines
link
attributes to entity
sets,
entity
sets to relationship sets
(also
represent
roles)
Double ellipses
represents
multi-
valued
attributes
Primary key attributes
are
EmpID
underlined.
Dashed ellipses
represent derived
attribute.
116
VU
Information
System (CS507)
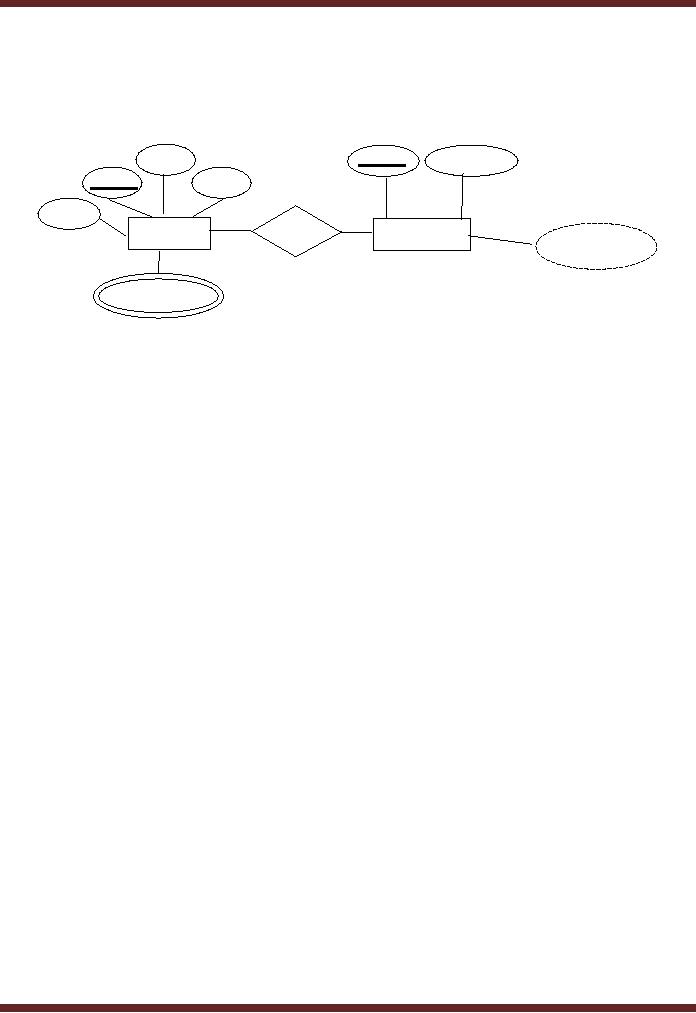
ERD
Example
Name
Dept.
ID
Dept.
Name
Emp.
ID
Phone
Hire
Date
Works
In
Employees
Departments
No. of
employees
College
Degree
The
diagram shows a primary relationship is
between two entities,
employee and the department.
The
relationship is of
an employee working in a department.
The figure also shows
information available
for
each
of these entities.
Object
Oriented Analysis and Design
(OOAD)
The
concept of object oriented analysis
and design focuses on
problems in terms of classes
and objects.
This
concept combines aspects of
both entity relationship diagram
and data flow diagrams.
The object
oriented
analysis and design tool
has been devised to support
the object oriented languages, for
example
C++
and Java. The roots of the
concept of object orientation evolved in
late 60's with the emergence
of
first
language "SIMULA 67" as the
first object oriented language.
Object oriented methodologies do
not
replace
traditional approaches (such as
data flow, process flow,
and state transition
diagrams); they are
important
new additions to the toolkit.
26.1
Why need Object-Orientation?
There
are certain positive points
which are becoming stronger
reasons for the increased
use of this
technique.
�
Object
orientation helps in increasing
abstraction and event-driven
programming
�
The
widespread use of Graphical
User Interface (GUI)
encourages use of object
orientation.
�
Software
can be developed on modular basis
1.
Easier to maintain
2.
Easier to upgrade
3.
Easier to test
4.
Easier to develop incrementally
�
Reusable
Software The software developed
using object oriented approach
can be easily reused
due to
independence/uniqueness of the objects
i.e. an independent accounting module
built in
object
oriented environment can be
made a part of a complete
ERP solution without developing
it
again
from scratch for
ERP.
26.2
Object Oriented Analysis
117

VU
Information
System (CS507)
The
concept of analysis has been
defined from different
perspectives in different approaches to
system
development.
"The
development activity consisting of the
discovery, modeling, specification and evaluation
of
requirements,"
Donald
Firesmith (Dictionary of Object Technology,
1995),
In
OOAD analysis has been
defined in a different manner
"The
discovery, analysis and specification of
requirements in terms of objects
with identity that
encapsulate
properties
and operations, message
passing, classes, inheritance,
polymorphism and dynamic
binding."
Object
oriented Design
The
concept of design has been
defined from different
perspectives in different approaches to
system
development.
"Systems
design is the process or art of defining
the hardware and software
architecture, components,
modules,
interfaces, and data for a
computer system to satisfy specified
requirements."
In
OOAD analysis has been
defined in a different manner.
According to Firesmith
"The
design of an application in terms of
objects, classes, clusters,
frameworks and their interactions
is
called
OOAD Analysis."
Basic
Concepts
Following
are the basic concepts
related to this technique.
An
object is defined as
"an
abstraction of something in a problem
domain, reflecting the capabilities of the system to
keep
information
about it, interact with it, or
both."
Coad
and Yourdon (1990)
An object is
any abstraction that models
a single concept.
Another
Definition of object
"A
concept, abstraction, or thing
with crisp boundaries and
meaning of the problem at hand.
Objects serve
two
purposes. They promote understanding of
the real world and provide a
practical basis for
computer
implementation."
Rumbaugh
et al. (1991)
Components of
object
According
to Booch, there are three
components of object. Objects have
state, behavior and
identity.
�
Identity:
Who is it?
Each
object has unique identity.
�
Behavior:
What can it do?
What
an object can do, how it can
respond to events and
stimuli.
118
VU
Information
System (CS507)
�
State:
What does it know?
The
condition of an object at any moment, affecting
how it can behave
Real-world
objects share two
characteristics: They all have
state and behavior.
For
example,
� Dogs
have state (name, color,
breed, hungry) and behavior (barking,
fetching, wagging tail).
� Bicycles
have state (current gear, current
pedal cadence, two wheels,
number of gears) and
behavior
(braking,
accelerating, slowing down, changing
gears).
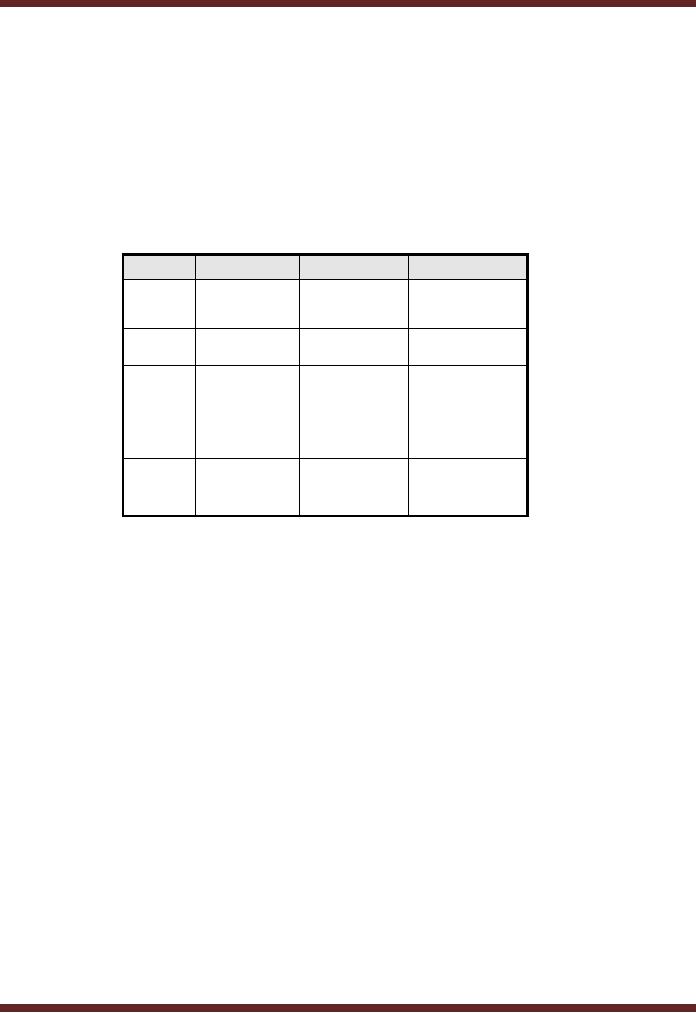
Objects
Object
Identity
Behaviour
States
`Ahmad'
Speak,
walk,
Studying,
resting,
A
qualified,
working.
read,
eat, talk,
person.
think.
white
denim
Shrink,
stain,
Pressed,
dirty,
A
shirt.
shirt
rip.
worn.
Invoiced,
Company:
Transaction
no.
A
sale.
Generate
060501 &
date
June
12, 2006
mode of
payment:
income.
cash/credit
Customer:
Earn
Bonus
points/Rebates
Adds
tang to the Unsold,
opened,
A bottle
Tomato,
garlic,
chilli
ketchup
meal
empty,
spilt in
of
transit
ketchup.
Examples
Software
objects are modeled after
real-world objects in that they
too have state and behavior.
We might
want to
represent real-world dogs as
software objects in an animation program or a
real-world bicycle as
software
object in the program that controls an electronic
exercise bike.
Classes
A
class is defined as
"The
purpose of a class is to specify a
classification of objects and to
specify the features that
characterize
the
structure and behavior of
those objects."
A
class is any uniquely
identified abstraction, that
is, model of a set of logically related
objects that share
the
same
or similar characteristics. The
purpose of a class is to specify a
classification of objects and to
specify
the
features that characterize the
structure and behavior of
those objects.
An object is an
instance of some class. All
objects are instances of
some class. Instance also
carries
connotations of the
class to which the object
belongs.
For
example, computers are the domain/Class
which can be divided into
following sub-classes:
� Laptop
computer
� Desktop
computer
� Palmtop
In the
sub-sub-class of laptops, we may
identify various laptop
models or brands which may
then have a
further
division on a model-wise
basis.
119

VU
Information
System (CS507)
120
Table of Contents:
- Need for information, Sources of Information: Primary, Secondary, Tertiary Sources
- Data vs. Information, Information Quality Checklist
- Size of the Organization and Information Requirements
- Hierarchical organization, Organizational Structure, Culture of the Organization
- Elements of Environment: Legal, Economic, Social, Technological, Corporate social responsibility, Ethics
- Manual Vs Computerised Information Systems, Emerging Digital Firms
- Open-Loop System, Closed Loop System, Open Systems, Closed Systems, Level of Planning
- Components of a system, Types of Systems, Attributes of an IS/CBIS
- Infrastructure: Transaction Processing System, Management Information System
- Support Systems: Office Automation Systems, Decision Support Systems, Types of DSS
- Data Mart: Online Analytical Processing (OLAP), Types of Models Used in DSS
- Organizational Information Systems, Marketing Information Systems, Key CRM Tasks
- Manufacturing Information System, Inventory Sub System, Production Sub System, Quality Sub system
- Accounting & Financial Information Systems, Human Resource Information Systems
- Decision Making: Types of Problems, Type of Decisions
- Phases of decision-making: Intelligence Phase, Design Phase, Choice Phase, Implementation Phase
- Planning for System Development: Models Used for and Types of System Development Life-Cycle
- Project lifecycle vs. SDLC, Costs of Proposed System, Classic lifecycle Model
- Entity Relationship Diagram (ERD), Design of the information flow, data base, User Interface
- Incremental Model: Evaluation, Incremental vs. Iterative
- Spiral Model: Determine Objectives, Alternatives and Constraints, Prototyping
- System Analysis: Systems Analyst, System Design, Designing user interface
- System Analysis & Design Methods, Structured Analysis and Design, Flow Chart
- Symbols used for flow charts: Good Practices, Data Flow Diagram
- Rules for DFD’s: Entity Relationship Diagram
- Symbols: Object-Orientation, Object Oriented Analysis
- Object Oriented Analysis and Design: Object, Classes, Inheritance, Encapsulation, Polymorphism
- Critical Success Factors (CSF): CSF vs. Key Performance Indicator, Centralized vs. Distributed Processing
- Security of Information System: Security Issues, Objective, Scope, Policy, Program
- Threat Identification: Types of Threats, Control Analysis, Impact analysis, Occurrence of threat
- Control Adjustment: cost effective Security, Roles & Responsibility, Report Preparation
- Physical vs. Logical access, Viruses, Sources of Transmissions, Technical controls
- Antivirus software: Scanners, Active monitors, Behavior blockers, Logical intrusion, Best Password practices, Firewall
- Types of Controls: Access Controls, Cryptography, Biometrics
- Audit trails and logs: Audit trails and types of errors, IS audit, Parameters of IS audit
- Risk Management: Phases, focal Point, System Characterization, Vulnerability Assessment
- Control Analysis: Likelihood Determination, Impact Analysis, Risk Determination, Results Documentation
- Risk Management: Business Continuity Planning, Components, Phases of BCP, Business Impact Analysis (BIA)
- Web Security: Passive attacks, Active Attacks, Methods to avoid internet attacks
- Internet Security Controls, Firewall Security SystemsIntrusion Detection Systems, Components of IDS, Digital Certificates
- Commerce vs. E-Business, Business to Consumer (B2C), Electronic Data Interchange (EDI), E-Government
- Supply Chain Management: Integrating systems, Methods, Using SCM Software
- Using ERP Software, Evolution of ERP, Business Objectives and IT
- ERP & E-commerce, ERP & CRM, ERP– Ownership and sponsor ship
- Ethics in IS: Threats to Privacy, Electronic Surveillance, Data Profiling, TRIPS, Workplace Monitoring