 |
NETWORKING DEVICES |
| << HOW MANY CLASS A, B, C NETWORKS AND HOSTS ARE POSSIBLE |
| BASICS OF HTML 1 >> |
E-COMMERCE
IT430
VU
Lesson
04
NETWORKING
DEVICES
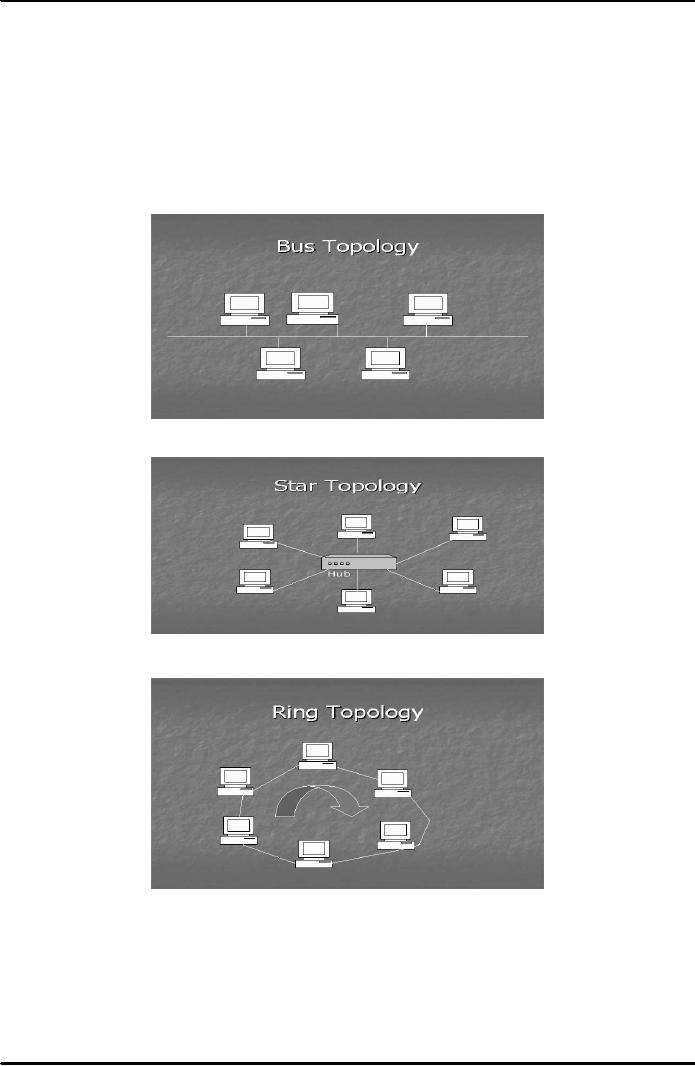
Topology
of a LAN means its physical
lay out. There are three
main types of Network
Topology, namely,
Bus
Topology, Star Topology and
Ring Topology as shown in Figures
1-3 below. There are two
different
approaches
to networking Server-based and
Peer-to-Peer approach. In server-based
approach there is a
centralized
server machine that can
serve users' requests for
the sharing of resources on a
network.
Contrarily,
in peer-to-peer, the machines on the
network have an equal capability
which means that they
can
act
both as a client and a
server.
Fig.
1
Fig.
2
Fig.
3
14
E-COMMERCE
IT430
VU
Networking
devices
Hubs
These
provide central connection point
for a LAN. They organize
cables and relay data
signals to all
computers.
There are ports on the back of a hub
used to connect computers. They
come in different
sizes
and
shapes.
Repeaters
Repeaters
regenerate signals. A repeater
would amplify the entire electric
signal it receives. However, it
has
no
capabilities of directing network
traffic.
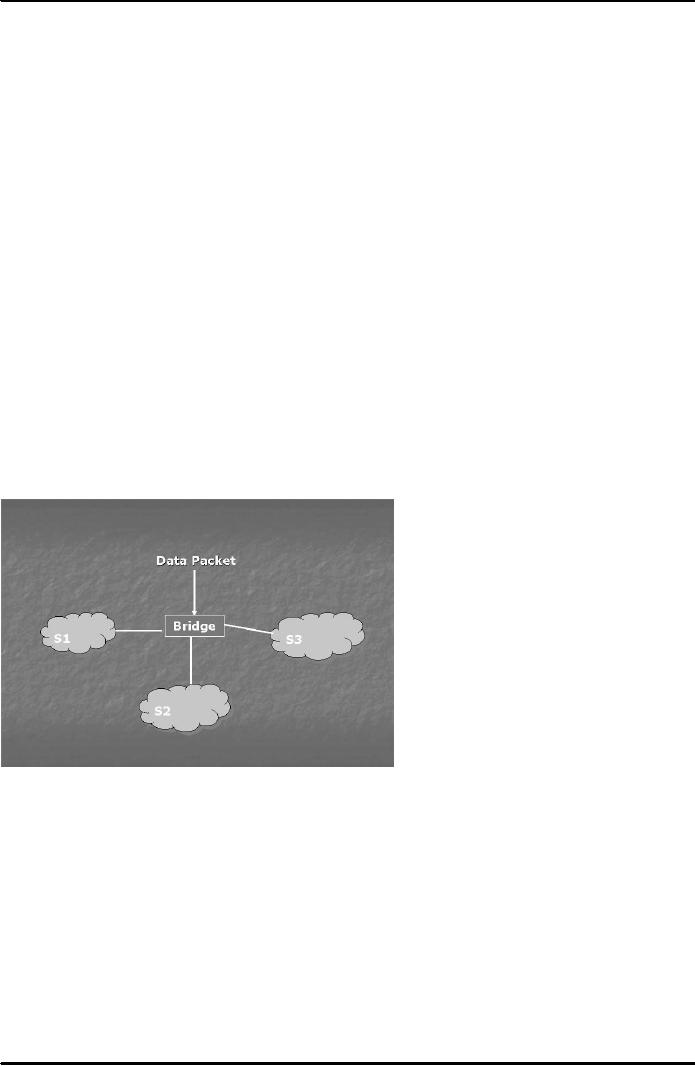
Bridges
A Bridge is a
combination of hardware and
software. It has its own
operating system. It helps to
conserve
the
bandwidth of a network. Bandwidth is the
speed of a network. It indicates
how many bits can be
transmitted
across a network in a given time. In case
of a bridge, the larger network is
physically chopped
into
smaller segments. A bridge can
read the MAC (Media Access
Control) or physical address of
a
computer on
data packets. MAC address is
printed on the Network Interface
Card. A bridge matches this
MAC
address with the one stored
in its table and judges that
which particular segment does a
data packet
belong to
and accordingly sends that
packet to such a segment. It
does not allow other
packets belonging to
other
segments to spread to a particular
segment and hence conserves
the bandwidth.
(See Fig. 4 below)
Fig.
4
Switches
A
switch is also a combination of
hardware and software having
its own operating system.
Like bridges, the
switches
are also used to increase
the bandwidth of a network. However, in
case of a switch, a network
is
virtually
divided into small segments
called Virtual LANs or
VLANs. Similar type of users
can be grouped
into a
VLAN despite that they have no
physical proximity or closeness. A
switch would read the
MAC
address
on a data packet and match
it with the list of MAC addresses of the
user machines contained in it.
It
then
sends data packets only to
that machine on a VLAN to which
these packets relate.
Packets belonging
to
other VLANs are not allowed
to enter into a particular VLAN,
hence bandwidth
increases.
Routers
Routers
use a combination of hardware
and software to forward data
packets to their destination on
the
15
E-COMMERCE
IT430
VU
internet.
They are more efficient
and sophisticated than
bridges and switches. They
can divide large
networks
into logical segments called
Subnets on the basis of IP addressing
scheme. A router can
communicate
with another router on the internet
with the help of Routing
Information Protocol, and
thus
it can
build a routing table. This
routing table contains
information about different
network addresses and
different
routes for delivery of data
packets to a host machine on a
network. A router is a decision
making
device.
When a data packet arrives
at a router it reads the network
addresses from the IP address on
the
data
packet and determines the
shortest possible path
through which this packet
can be delivered to its
destination.
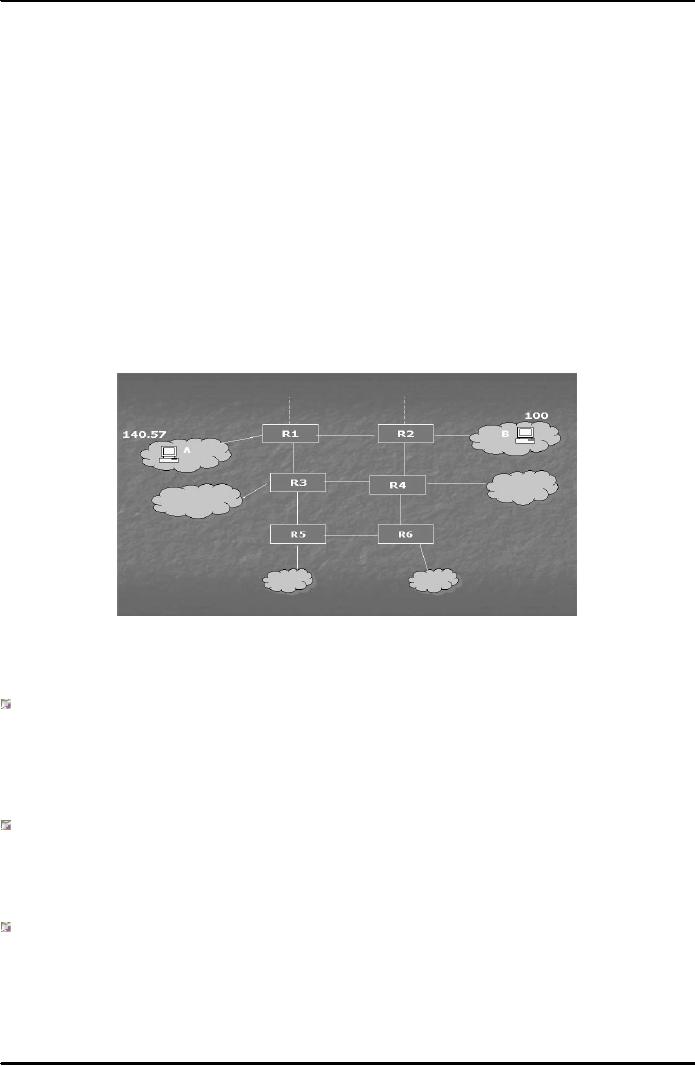
Following
diagram (Fig. 5) explains how
routers on the internet backbone
forward data packets
by
determining the
shortest possible path for
the destination. In this example a client
machine `A' sitting
on
network
no. 140.57 sends data to a
web server `B' hosted at
network no. 100. `R1' is the
router attached to
network
no. 140.57. After consulting
its routing table it can
find that the shortest
possible path for
sending
data
to machine `B' is to forward
data packets to `R2', the
router attached to network
no. 100. In case
there
is a
blockade then`R1' can look
for the alternative shortest path. Here,
the alternative shortest path for
the
delivery of
data packets to `B' can be
R1-R3-R4-R2.
Fig.
5
Cabling
options
Cooper-based
cables
They
are quite commonly used for
connecting computers. They have two
main types coaxial and
twisted
pair. In twisted
pair there are two
further options unshielded twisted
pair (UTP) and Shielded
Twisted
Pair
(STP).
Fiber optic
cables
They
are used on the internet. They
deliver data at a very high
speed. They use glass or
plastic filaments and
the
pulses of light as a data
transfer method.
Telephone
and electrical wire networks
They
can also be used for
connectivity purpose.
Wireless
options
Wireless
options include radio connectivity
(wi fi, bluetooth), infrared
connectivity and Satellite
microwave
16
E-COMMERCE
IT430
VU
transmissions.
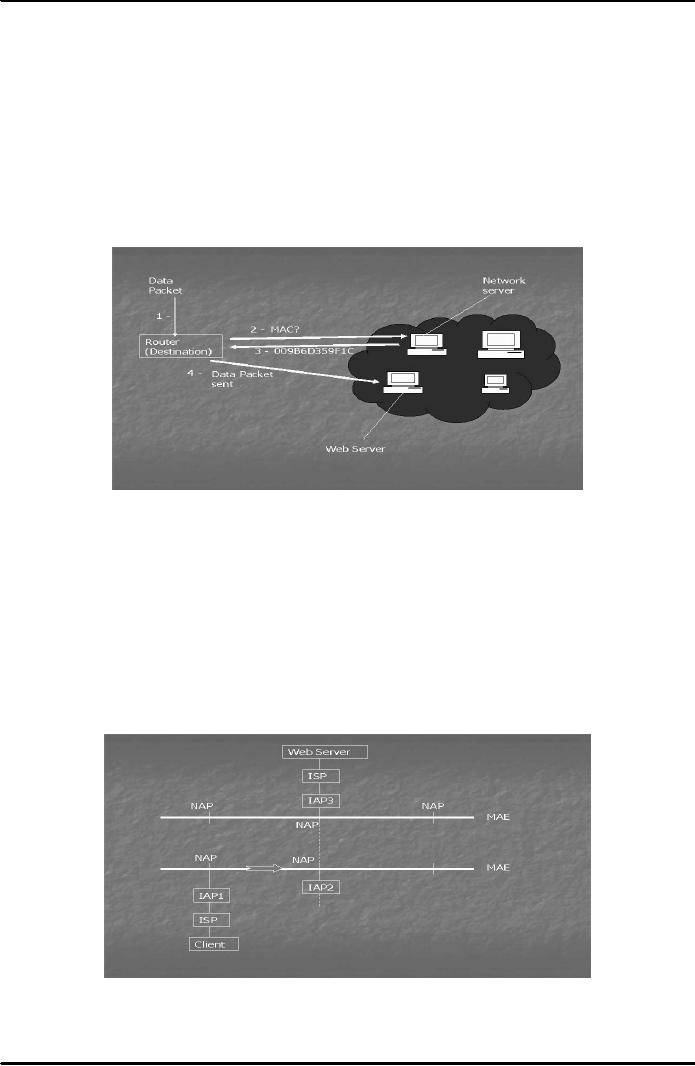
Address
resolution protocols (ARP) and
address resolution protocol
(RARP)
Each
computer on the internet prepares a list
of its IP address and corresponding MAC
address using ARP.
Through
RARP this information is forwarded to a network
server. When a data packet
arrives at the
destination
router, it inquires about the corresponding MAC
address form the network
server, inserts it
and
delivers
the packet to that MAC address. A
data packet therefore needs
both IP and MAC addresses
to
reach
its destination. (See Fig. 6
below)
Fig.
6
Role
of ISPs on internet
Internet
Service Providers (ISPs) are
those organizations which
can provide internet
connections, offer
services
of web hosting, newsgroups and
internet e-mail etc. They
work in a hierarchy. The ISP at the
top of
the
hierarchy which is connected
with internet backbone is
called Internet Access
Provider or IAP. An
internet
trunk line or backbone
passing through a metropolitan
area is also called
Metropolitan Area
Ethernet
(MAE). IAPs are connected to
MAEs at points called
Network Access Points (NAPs).
Trunk lines
allow
IAPs to move data. The
actual routing of data
packets takes place on
internet backbone (see
Fig. 7
below).
Fig.
7
17
Table of Contents:
- E-COMMERCE
- WHAT IS A NETWORK
- HOW MANY CLASS A, B, C NETWORKS AND HOSTS ARE POSSIBLE
- NETWORKING DEVICES
- BASICS OF HTML 1
- BASICS OF HTML 2
- TEXT BOXES, CHECK BOXES, RADIO BUTTONS
- FRAMES AND IMAGES IN HTML
- TAG ATTRIBUTES, SOUNDS FILES, ANIMATIONS
- STYLE SHEETS 1
- STYLE SHEETS 2
- SOME USEFUL STYLE SHEETS PROPERTIES
- JAVA SCRIPTING 1
- JAVA SCRIPTING 2
- JAVA SCRIPTING 3
- JAVA SCRIPTING AND XML
- CLIENT AND SERVER SIDE PROCESSING OF DATA
- APPLETS, CGI SCRIPTS
- MAINTAINING STATE IN A STATELESS SYSTEM
- INTEGRATION WITH ERP SYSTEMS
- FIREWALLS
- CRYPTOGRAPHY
- HASH FUNCTION AND MESSAGE DIGEST
- SYMMETRIC KEY ALGORITHMS
- VIRTUAL PIN PAYMENT SYSTEM
- E-CASH PAYMENT SYSTEM 1
- E-CASH PAYMENT SYSTEM 2
- SECURE SOCKET LAYER (SSL)
- E-BUSINESS: DISADVANTAGES OF E-BUSINESS
- E-BUSINESS REVENUE MODELS
- E-MAIL MARKETING
- CUSTOMER RELATIONSHIP MANAGEMENT (CRM)
- META INFORMATION
- DATA MINING
- CONFIDENCE AND SUPPORT
- ELECTRONIC DATA INTERCHANGE (EDI)
- PERSONAL FINANCE ONLINE
- SUPPLY CHAIN
- PORTER’S MODEL OF COMPETITIVE RIVALRY
- BARRIERS TO INTERNATIONAL E-COMMERCE
- ELECTRONIC TRANSACTIONS ORDINANCE, 2002 - 1
- ELECTRONIC TRANSACTIONS ORDINANCE, 2002 - 2
- ELECTRONIC TRANSACTIONS ORDINANCE, 2002 - 3
- GLOBAL LEGAL ISSUES OF E-COMMERCE - 1
- GLOBAL LEGAL ISSUES OF E-COMMERCE - 2