 |
VU
Information
System (CS507)
The
first increment is usually the core
product which addresses the
basic requirements of the system.
This
maybe
either be used by the client or subjected to
detailed review to develop a plan for the
next increment.
This plan
addresses the modification of the core
product to better meet the needs of the
customer, and the
delivery of
additionally functionality. More
specifically, at each
stage
�
The
client assigns a value of
functionality to each module not
yet implemented
�
The
developer estimates cost of developing
each module
�
The
resulting value-to-cost ratio is the
criterion used for selecting
which module is delivered next
Essentially
the module with the highest value-to-cost
ratio is the one that provides the client
with the most
functionality
(value) for the least cost.
Using this method the client has a usable
product at all of the
development
stages. Modules are also
selected on the basis of the customer
requirements and needs
apart
from
the value to cost
ratio.
20.1
Characteristics of the Incremental
Model
�
The
system development is broken into
many mini development
projects
�
Partial
systems are successively
built to produce a final total
system.
�
Highest
priority requirements tackled
early on.
�
Once
an incremented portion is developed,
requirements for that increment
are frozen.
20.2
Incremental Model-Evaluation
Benefits
�
Working
functionality is produced earlier
computation of value to cost
ratio
�
Reduces
risks of change in user
requirements
�
Provides
clients flexibility in decision
making.
�
Risk
management is incremental
�
Smaller
scope for change in user
requirements
85

VU
Information
System (CS507)
Criticism
�
Larger
picture cannot be seen until the entire
system is built
�
Difficult
to break down the total
system at early stage of
product development to determine
reasonable
increments
Iterative
Models
Iterative
models are an approach for
developing systems based on
producing deliverables
frequently/repetitively.
Each iteration, consisting of
requirements, analysis & design,
implementation and
testing,
results in the release of an executable
subset of the final product.
These subsets grows
incrementally
from
iteration to iteration to become the
final system. The Procedure
itself consists of three
basic steps.
�
The
Initialization step -- creates a
base version of the system. The
goal for this initial
implementation is
to
create a product to which the
user can react.
�
The
Iteration step -- The
iteration step
involves
�
The
redesign and implementation of a
task from project control
list. The goal for the
design and
implementation
of any iteration is to be simple,
straightforward, and modular, supporting
redesign
at
that stage or as a task
added to the project control
list.
�
The
analysis of the current version of the system.
The analysis of an iteration is
based upon user
feedback
and the program analysis facilities
available. It involves analysis of the
structure,
modularity,
usability, reliability, efficiency, and
achievement of goals. The
project control list
is
modified
in light of the analysis
results.
�
The
Project Control List -- To
guide the iteration process, a
project control list is
created that
contains
a record of all tasks that
need to be performed. It includes
n
�
New
features to be implemented, and
�
Areas
of redesign of the exiting
solution.
The
control list is constantly being revised
as a result of the analysis
phase.
20.3
Iterative Models
Evaluation
Harms
The
Iterative Model can lead to
"scope creep," since user
feedback following each
phase may lead to
increased
customer demands. As users see the
system develop, they may realize the
potential of other
system
capabilities which would
enhance their work.
Benefits
�
In
fact, the context of multiple iterations
provides advantages in the use of
measuring various
aspects
of
product development, such as
�
Effort
to date
�
Changes,
�
Defects,
�
Logical,
physical, and dynamic
attributes,
�
Environmental
considerations.
86

VU
Information
System (CS507)
�
The
customer can tell how
product characteristics like
size, complexity, coupling, and cohesion
are
increasing
or decreasing over time.
�
One
can monitor the relative change of the
various aspects of the product or
can provide bounds
for
the
measures to signal potential
problems and
anomalies.
20.4
Incremental vs.
Iterative
These
sound similar, and sometimes
are equated but there is a
subtle difference:
�
Incremental:
add to the product at each
phase
�
Iterative:
re-do the product at each
phase
Example
Building
a House
�
Incremental:
Starts with a modest house,
keep adding rooms and
upgrades to it.
�
Iterative:
The design/construction map of the
house is amended and
improved and repeated
until
all the requirements are
fulfilled.
87
Table of Contents:
- Need for information, Sources of Information: Primary, Secondary, Tertiary Sources
- Data vs. Information, Information Quality Checklist
- Size of the Organization and Information Requirements
- Hierarchical organization, Organizational Structure, Culture of the Organization
- Elements of Environment: Legal, Economic, Social, Technological, Corporate social responsibility, Ethics
- Manual Vs Computerised Information Systems, Emerging Digital Firms
- Open-Loop System, Closed Loop System, Open Systems, Closed Systems, Level of Planning
- Components of a system, Types of Systems, Attributes of an IS/CBIS
- Infrastructure: Transaction Processing System, Management Information System
- Support Systems: Office Automation Systems, Decision Support Systems, Types of DSS
- Data Mart: Online Analytical Processing (OLAP), Types of Models Used in DSS
- Organizational Information Systems, Marketing Information Systems, Key CRM Tasks
- Manufacturing Information System, Inventory Sub System, Production Sub System, Quality Sub system
- Accounting & Financial Information Systems, Human Resource Information Systems
- Decision Making: Types of Problems, Type of Decisions
- Phases of decision-making: Intelligence Phase, Design Phase, Choice Phase, Implementation Phase
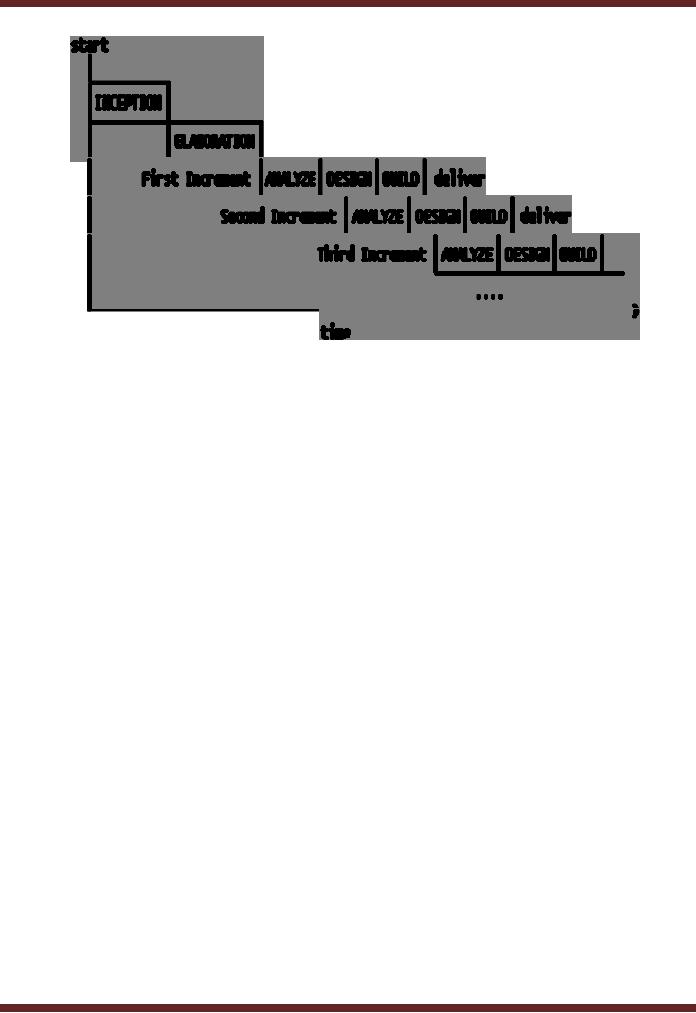
- Planning for System Development: Models Used for and Types of System Development Life-Cycle
- Project lifecycle vs. SDLC, Costs of Proposed System, Classic lifecycle Model
- Entity Relationship Diagram (ERD), Design of the information flow, data base, User Interface
- Incremental Model: Evaluation, Incremental vs. Iterative
- Spiral Model: Determine Objectives, Alternatives and Constraints, Prototyping
- System Analysis: Systems Analyst, System Design, Designing user interface
- System Analysis & Design Methods, Structured Analysis and Design, Flow Chart
- Symbols used for flow charts: Good Practices, Data Flow Diagram
- Rules for DFD’s: Entity Relationship Diagram
- Symbols: Object-Orientation, Object Oriented Analysis
- Object Oriented Analysis and Design: Object, Classes, Inheritance, Encapsulation, Polymorphism
- Critical Success Factors (CSF): CSF vs. Key Performance Indicator, Centralized vs. Distributed Processing
- Security of Information System: Security Issues, Objective, Scope, Policy, Program
- Threat Identification: Types of Threats, Control Analysis, Impact analysis, Occurrence of threat
- Control Adjustment: cost effective Security, Roles & Responsibility, Report Preparation
- Physical vs. Logical access, Viruses, Sources of Transmissions, Technical controls
- Antivirus software: Scanners, Active monitors, Behavior blockers, Logical intrusion, Best Password practices, Firewall
- Types of Controls: Access Controls, Cryptography, Biometrics
- Audit trails and logs: Audit trails and types of errors, IS audit, Parameters of IS audit
- Risk Management: Phases, focal Point, System Characterization, Vulnerability Assessment
- Control Analysis: Likelihood Determination, Impact Analysis, Risk Determination, Results Documentation
- Risk Management: Business Continuity Planning, Components, Phases of BCP, Business Impact Analysis (BIA)
- Web Security: Passive attacks, Active Attacks, Methods to avoid internet attacks
- Internet Security Controls, Firewall Security SystemsIntrusion Detection Systems, Components of IDS, Digital Certificates
- Commerce vs. E-Business, Business to Consumer (B2C), Electronic Data Interchange (EDI), E-Government
- Supply Chain Management: Integrating systems, Methods, Using SCM Software
- Using ERP Software, Evolution of ERP, Business Objectives and IT
- ERP & E-commerce, ERP & CRM, ERP– Ownership and sponsor ship
- Ethics in IS: Threats to Privacy, Electronic Surveillance, Data Profiling, TRIPS, Workplace Monitoring