 |
AN INDUSTRY IN DENIAL, SUCCESS CRITERIA IN THE NEW ECONOMY |
| << DEFINITION OF HCI, REASONS OF NON-BRIGHT ASPECTS, SOFTWARE APARTHEID |
| GOALS & EVOLUTION OF HUMAN COMPUTER INTERACTION >> |

Human
Computer Interaction
(CS408)
VU
Lecture
3
Lecture 3.
Introduction
to
Human-
Computer
Interaction Part III
Learning
Goals
As the
aim of this lecture is to
introduce you the study of
Human Computer
Interaction,
so that after studying this
you will be able to:
Discuss
the effect of bad
tools
·
Discuss
and argue about why Human
computer Interaction (HCI) is
important
·
with
reference to the way in
which technology has
developed during past
forty
years
Describe
requirement of new economy
era.
·
Effect of
Bad Tools
Not
only are computers taking
over the cockpit of jet
airliners, they are taking
over
the
passenger cabin, too,
behaving in that same
obstinate, perverse way that is so
easy
to
recognize and so hard to
use. Modern jet planes have
in-flight entertainment
(IFE)
systems
that deliver movies and
music to airline passengers.
These IFEs are
merely
computers connected
with local area network,
just like in your office.
Advanced IFE
systems
are generally installed only on
larger airplanes flying transoceanic
routes.
One
airline's IFE was so
frustrating for the flight
attendants to use that many of
them
were
bidding to fly shorter, local
routes to avoid having to
learn and use the
difficult
systems.
This is remarkable considering
that the time-honored
airline route-bidding
process
is based on seniority, and
that those same
long-distance routes have
always
been
considered the most desirable
plums because of their
lengthy layovers in
exotic
locales
like Singapore or Paris. For
flight attendants to bid for
unglamorous,
unromantic
yo-yo flights from
Denver-to-Dallas or LA-to-San Francisco
just to avoid
the
IFE indicated a serious morale
problem. Any airline that
inflicted bad tools on
its
most
prized employee--the ones
who spent the most time with
the customer---was
making a
foolish decision and was
profligately discarding money, customer
loyalty,
and
staff loyalty.
The
computer-IFE of another large
airline was even worse.
The airline had created
an
in-flight
entertainment system that
linked movie delivery with
the cash collection
function.
In a sealed et airplane flying at
37,000 feet, cash collection
procedures had
typically
been quite laissez-faire; after
all, nobody was going to
sneak out the back
door.
Flight attendants delivered goods
and services when it was
convenient and
collected
cash in only a very loosely
coupled fashion. This kept
them from running
unnecessarily
up and down the narrow
aisles. Sure there were occasional
errors, but
21

Human
Computer Interaction
(CS408)
VU
never
more than a few dollars
were involved, and the
system was quite human
and
forgiving;
everyone was happy and
the work was not
oppressive.
With
cash-collection connected to content
delivery by computer, the
flight attendant
had to
first get the cash
from the passenger, then
walk all the way to
the head-end of
the
cabin, where the attendant's
console was, enter an
attendant password, then
perform a
cash register-like transaction.
Only when that transaction
was completed
could
the passenger actually view
a movie or listen to music.
This inane product
design
forced the flight attendants to
walk up and down those
narrow aisles hundreds
of extra
times during a typical trip.
Out of sheer frustration,
the flight attendants
would
trip the circuit breaker on
the in-flight entertainment
system at the beginning
of
each
long flight, shortly after
departure. They would then
blandly announce to
the
passengers
that, sorry, the system
was broken and there
would be no movie on
this
flight.
The
airline had spent millions of
dollars constructing a system so
obnoxious that its
users
deliberately turned it off to
avoid interacting with it.
The thousands of bored
passengers
were merely innocent
victims. And this happened
on long, overseas
trips
typically
packed with much-sought-after
frequent flyers. I cannot
put a dollar figure
On the
expense this caused the
airline, but I can say
with conviction that it
was
catastrophically
expensive.
The
software inside the IFEs
worked with flawless
precision, but was a
resounding
failure
because it misbehaved with
its human keepers.
3.1
An
Industry in Denial
We are a
world awash in high-tech
tools. Computers dominate
the workplace and
our
homes,
and vehicles are filling up
with silicon-powered gadgets. All of
these
computerized
devices are wildly
sophisticated and powerful,
but every one of them
is
dauntingly
difficult and confusing to
use.
The
high-tech industry is in denial of a
simple fact that every
person with a cell
phone
or a word
processor can clearly see:
our computerized tools are
hard to use. The
technologists
who create software and
high-tech gadgets are satisfied with
their
efforts.
The software engineers who
create them have tried as
hard as they can to
make
them easy to use and
they have made some minor
progress. They believe
that
their
products are as easy to use
as it is technically possible to make
them. As
engineers,
their belief is in technology,
and they have faith
that only some
new
technology,
like voice recognition or
artificial intelligence, will improve
the user's
experience.
Ironically,
the thing that will likely
make the least improvement in
the ease of use of
software-based
products is new technology.
There is little difference
technically
between a
complicated, confusing program
and a simple, fun, and
powerful product.
The
problem is one of culture,
training, and attitude of
the people who make
them,
22

Human
Computer Interaction
(CS408)
VU
more
than it is one of chips and
programming languages. We are deficient
in our
development
process, not in out
development tools.
The
high-tech industry has
inadvertently put programmers
and engineers in charge, so
their
hard-to-use engineering culture
dominates. Despite appearances,
business
executives
are simply not the
ones in control of the
high-tech industry. It is
the
engineers
who are running the
show. In our rush to accept
the many benefits of
the
silicon
chip, we have abdicated our
responsibilities. We have let
the inmates run
the
asylum.
When
the inmates run the
asylum, it is hard for them
to see clearly the nature of
the
problems
that bedevil them. When
you look in the mirror, it
is all too easy to
single
out
your best features and
overlook the warts. When
the creators of software-based
products
examine their handiwork,
they see how rich
the product is in features
and
functions.
They ignore how
excruciatingly difficult it is to use,
how many mind-
numbing
hours it takes to learn, or how it
diminishes and degrades the
people who
must use
it in their everyday
lives.
3.2
Techno-Rage
An
article in a recent issue of the
Wall Street Journal described an
anonymous video
clip
circulated widely by email
that showed as "...Mustachioed
Everyman in a short
sleeved
shirt hunched over a
computer terminal, looking
puzzled. Suddenly, he
strikes
the side
of his monitor in frustration. As a
curious co-worker peers over
his cubicle,
the man
slams the keyboard into
the monitor, knocking it to
the floor. Rising from
his
chair, he
goes after the fallen
monitor with a final
ferocious kick." The article
went on
to say
that reaction to the clip
had been "intense" and that
it had apparently
tapped
into a
powerful undercurrent of
techno-rage".
It's
ironic that one needs to be
moderately computer savvy to
even send or view
this
video
clip. While the man in the
video may well be an actor,
he touches a widespread,
sympathetic
chord in out business world.
The frustration that
difficult and
unpleasant
software-based
products are bringing to our
lives is rising
rapidly.
Joke
email circulates on private
lists about "Computer
Tourette's." This is a play
on
the
disorder known as Tourette's
syndrome, where some
sufferers engage in
uncontrollable
bouts of swearing. The joke
is that you can walk
down the halls of
most
modern office buildings and
hear otherwise-normal people
sitting in front of
their
monitors, jaws clenched,
swearing repeatedly in a rictus of
tense fury. Who
knows
what triggered such an
outburst: a misplaced file, an
inaccessible image, or a
frustrating
interaction. Or maybe the
program just blandly erased
the user's only copy
of a
500-page manuscripts because he responded
with a "Yes" to a
confirmation
dialog
box, assuming that it had asked
him if he wanted to "save
your changes?"
when it
actually asked him if he
wanted to "discard your
work?"
Novatech
survey
One in
every four computers has been
physically attacked by its
owner, according to a
survey.
23

Human
Computer Interaction
(CS408)
VU
The
survey, conducted by British PC
manufacturer Novatech, was
intended to take a
lighthearted
look at embarrassing experiences -- those
little technical bloopers
that
happen
even to ubergeeks, like
forwarding a personal love
letter to an entire
office
mailing
list.
But
instead, a much darker story
emerged in the 4,200 replies.
Innocent computers are
being
beaten on a regular basis, often by
technically challenged users
who decide to
take
their frustrations out on
their helpless machines.
"We
decided to do some research
into people's relationships with
their computers and
we were
amazed by some of the
results," Novatech managing
director David Furby
said.
"As computers become more and
more a part of our daily
lives, we obviously
share
more experiences with
them."
Many
technical support people
from the United States,
Canada and parts of Europe
have
sobering stories of brutalized computers
being brought in for repair
by sad -- or
in some
cases, smug -- owners who
had smacked, kicked or
otherwise deliberately
injured
their machines.
"The
incidences of willful neglect
have always been high," said
David Tepper, owner
of the
Village Computer Shop in New
York. "We've always had to
deal with
computers damaged by
people who dumped their
refreshing beverage on
the
computer's
keyboard, or got tangled up in
the cords and bringing (sic)
the computer
crashing
down off their
desk."
"But
there have also always been
a small - but significant -
number of machines
that
were obviously intentionally
damaged."
"Hopefully
as technology improves and computers
become ever more user-
friendly,
these
attacks will become less frequent,"
Furby said.
Computer
rage
There is
a technology-based scourge afoot...maybe.
It's not a virus; it's
not a denial
of
service attack; it's
computer rage, and according to
the latest reports, it is
out to
destroy
the physical health, the
emotional stability, and if
left unchallenged,
the
economic
strength of whatever population it
strikes.
Security
software vendor Symantec,
working with Britain's
National Opinion
Poll,
recently
found that when confronted
with technical problems,
more than 40 percent
of
British
users surveyed have sworn
at, kicked, or otherwise
abused their
computers,
monitors,
and the most victimized of
all computer components,
their keyboards.
In
similar surveys conducted last
year, Marlborough, Mass-based
Concord
Communications
discovered that 83 percent of
150 U.S. respondents witnessed
such
attacks,
and the international market
research firm Mori found
that 40 percent of
1250
British
workers had watched as their
colleagues leveled verbal
and physical abuse at
their
computers.
24

Human
Computer Interaction
(CS408)
VU
Stress
related to computer rage, the
Symantec study claims, has
resulted in a loss of
productivity
for most respondents.
Robert
Edelmann, clinical psychologist
and author of Interpersonal
Conflicts at Work,
is
worried. "Frustration with IT
should be taken seriously as a
modern malaise," he
says. "It
is affecting both our work
and our home lives to
the extent that
computer
rage is
now much more prolific
than road rage."
Computers
increasingly commonplace in
offices
As the
reliance on computers in the workplace
continues to grow, people in
the UK
are
resorting to violence when
their PCs break down,
say researchers. When
faced
with
technical problems, most people
shouted at colleagues, hit
the PC or even threw
parts of
the computers. The most
frustrating hitch was when
people lost their
work
after
their computer crashed or
froze.
The
problems seem to be widespread
with more than a quarter of
those working with
computers
experience problems with
their PC on a weekly
basis.
"Over
half of all working days
lost to sickness in the UK
are related to
workplace
stress,"
said Fiona Dennis, a stress
management trainer with Priory
Healthcare.
"Being
heavily reliant on IT to speed up
our lives means that
performance is
hampered
greatly when it fails,
causing an over-reaction and
stress."
70% swear at
PCs
The
study by the National
Opinion Poll and the
software company Symantec,
found
that
nearly half of all computer
users had become angry at
some time. Almost a
third
of people
had physically attacked a
computer, 67% experienced
frustration,
exasperation
and anger and more
than 70% swore at their
machines.
Technology
rage is the latest rage to emerge in
Britain and follows road
rage, trolley
rage and
air rage. There was a
dramatic rise in air rage
incidents last year, with
174
people
detained at Heathrow and
Gatwick alone. In 1998 the
number of air rage
arrests
for the whole country
was 98.
3.3
Success
Criteria in the New
Economy
The
successful professional for
the twenty-first century is
either a business
savvy
technologist
or a technology-savvy businessperson.
The
technology-savvy businessperson knows
that his success is
dependent on the
quality
of the information available to
him and the sophistication
with which he uses
it.
The business-savvy technologist, on the
other hand, is an entrepreneurial
engineer
or
scientist trained for
technology, but possessing a
knee business sense and
an
awareness
of the power of information.
Both of these new archetypes are
coming to
dominate
contemporary business.
You
can divide all businesspeople
into two categories: those
who will master high
technology
and those who will soon be going
out of business. No longer
can
25

Human
Computer Interaction
(CS408)
VU
executive
delegate information processing to specialists.
Business is information
processing.
You differentiate yourself
today with the quality of
your information-
handling
systems, not your
manufacturing systems. If you
manufacture anything,
chances
are it has a microchip in
it. If you offer a service,
odds are that offer it
with
computerized
tools. Attempting to identify
businesses that depend on
high technology
is as
futile as trying to identify
businesses that depend on
the telephone. The
high-tech
revolution
has invaded every business,
and digital information is
the beating heart of
your
workday.
It has
been said, "to err is human;
to really screw up, you need
a computer."
Inefficient
mechanical systems can waste
couple cents on every widget
you build, but
you
can lose your entire company
to bad information processes.
The leverage that
software-based
products---and the engineers
that build them---have on
your company
is
enormous.
Sadly,
our digital tools are
extremely hard to learn,
use, and understand, and
they
often
cause us to fall short of
our goals. This wastes
money, time, and
opportunity. As
a
business-savvy technologist/
technology-savvy businessperson, you
produce
software-based
products or consume them---probably both.
Having better,
easier-to-
learn,
easier-to-use high-tech products is in
your personal and
professional best
interest.
Better products don't take
longer to create, nor do they
cost more to build.
The
irony is that they don't
have to be difficult, but
are so only because our
process
for
making them is old-fashioned
and needs fixing. Only
long-standing traditions
rooted in
misconceptions keep us from
having better products in
today.
Consider
a scenario: a website is developed of
ecommerce system. The site
is
aesthetically
very beautiful, technically it
has no flaw and it has
wonderful animated
content
on it. But if user is unable
to find its desired
information about the
products or
even he
is unable to find the
product out of thousands of products, so
what of it's use.
It is
useless from the business
point of view.
Here are some facts and
figures:
Users can
only find information 42% of
the time
Jared
Spool
62% of
web shoppers give up looking
for the item they
want to buy online
Zona Research
50% of
the potential sales from a
site are lost because
people cannot find the
item they
are
looking for
Forrester Research
40% of
the users who do not
return to a site do so because
their first visit resulted
in a
negative
experience
Forrester Research
26
Human
Computer Interaction
(CS408)
VU
80% of
software lifecycle costs
occur after the product is
released, in the maintenance
phase -
of that work, 80 % is due to
unmet or unforeseen user
requirements; only 20
% is due
to bugs or reliability problems.
- IEEE
Software
Around
63% of software projects exceed
their cost estimates. The
top four reasons
for
this
are:
Frequent requests for
changes from users
Overlooked tasks
Users'
lack of understanding of their
own requirements
Insufficient user-analyst communication
and understanding
-
Communications of the ACM
BOO.com,
a $204m startup fails
BBC
News
Poor
commercial web sites will kill
80% of Fortune 500 companies
within a decade
- Jakob
Nielsen
So all
above given facts reveals
that the product with
the bad user experience
deserve
to
die!
The
serious financial implications of today's
digital products should not
in any ways
be
underestimated.
The
table given below depicts
two scenarios of potential of
sales from an e-commerce
web
site. In scenario A, users
can easily find items
they are looking for, so 0%
sales
are lost,
so the actual revenue is
$100 million. In scenario B, users
cannot easily find
the
items they are looking for,
therefore, the actual
revenue is $50 million,
thus
causing a
loss of $50 million.
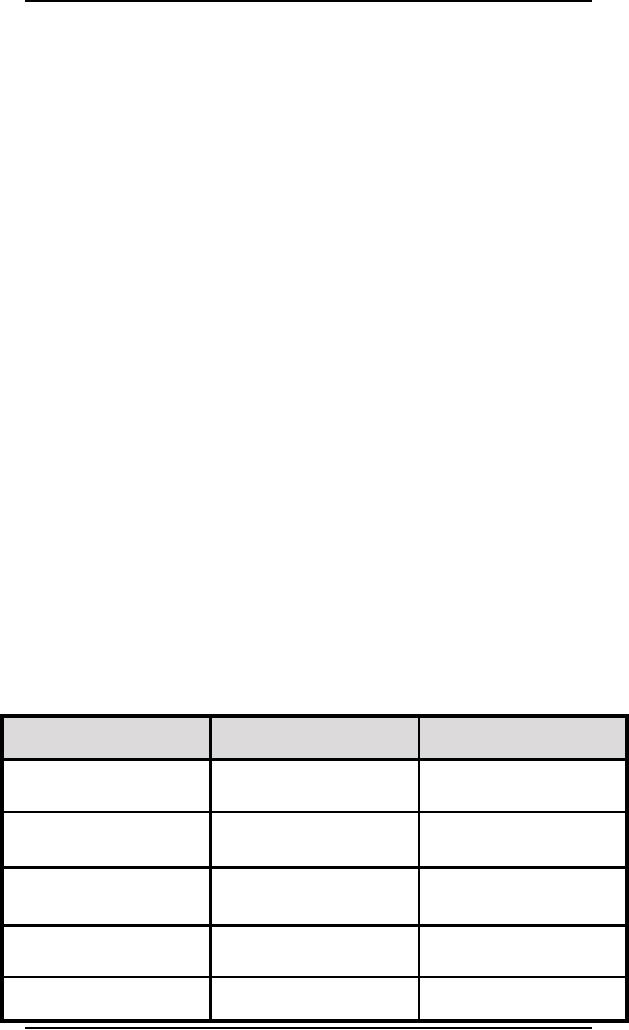
Scenario
A
Scenario
B
Revenue
Potential
$100m
$100m
User
Experience
Good
Bad
Sales
Lost
0%
50%
Revenue
Lost
$0m
$50m
Actual
Revenue
$100m
$50m
27

Human
Computer Interaction
(CS408)
VU
3.4
Computer
+ Information
What do
you get when you
cross a computer with
information?
In 2000,
the Olympic Games were
held in Sydney. Before the
Olympic games could
begin, a
lawsuit was filed against
the Olympic Committee. The
case was called
Bruce
Lindsay
Maguire vs Sydney Organizing
Committee for the Olympics
Games
(SOCOG).
On 7 June 1999 the complainant,
who is blind, complained to
the
Commission
that he was unlawfully
discriminated against by the
respondent in three
respects:
the
failure to provide Braille copies of
the information required to
place orders
·
for
Olympic Games
tickets;
the
failure to provide Braille copies of
the Olympic Games
souvenir
·
programmed;
and
The
failure to provide a web
site which was accessible to
the complainant.
·
It was
alleged that the SOCOG
was in breach the Disability
Discrimination Act 1992
by
failing to make accessible to
him key parts of its web
site
According
to the law of many European
and western countries,
organizations with a
web
site must ensure that their
web site is (within certain
limits) accessible by
disabled
persons. However, this was
not the case in the
matter of the official
Olympic
Games
web site. Could this
have been avoided? Certainly: by
applying a few very
simple
techniques, the developers of
the web site could
have made it accessible to
people
with vision-impairment. But as is
usually the case, this
was not done.
Result:
the complainant won the
case and was awarded a
sum of money in
damages.
This
was very embarrassing for
both the SOCOG and
also the company
that
developed
the web site.
References
1.
http://www.independentliving.org/docs5/sydney-olympics-blind-accessibility-
decision.html
2. http://comment.cio.com/soundoff/061400.html
28
Table of Contents:
- RIDDLES FOR THE INFORMATION AGE, ROLE OF HCI
- DEFINITION OF HCI, REASONS OF NON-BRIGHT ASPECTS, SOFTWARE APARTHEID
- AN INDUSTRY IN DENIAL, SUCCESS CRITERIA IN THE NEW ECONOMY
- GOALS & EVOLUTION OF HUMAN COMPUTER INTERACTION
- DISCIPLINE OF HUMAN COMPUTER INTERACTION
- COGNITIVE FRAMEWORKS: MODES OF COGNITION, HUMAN PROCESSOR MODEL, GOMS
- HUMAN INPUT-OUTPUT CHANNELS, VISUAL PERCEPTION
- COLOR THEORY, STEREOPSIS, READING, HEARING, TOUCH, MOVEMENT
- COGNITIVE PROCESS: ATTENTION, MEMORY, REVISED MEMORY MODEL
- COGNITIVE PROCESSES: LEARNING, READING, SPEAKING, LISTENING, PROBLEM SOLVING, PLANNING, REASONING, DECISION-MAKING
- THE PSYCHOLOGY OF ACTIONS: MENTAL MODEL, ERRORS
- DESIGN PRINCIPLES:
- THE COMPUTER: INPUT DEVICES, TEXT ENTRY DEVICES, POSITIONING, POINTING AND DRAWING
- INTERACTION: THE TERMS OF INTERACTION, DONALD NORMANS MODEL
- INTERACTION PARADIGMS: THE WIMP INTERFACES, INTERACTION PARADIGMS
- HCI PROCESS AND MODELS
- HCI PROCESS AND METHODOLOGIES: LIFECYCLE MODELS IN HCI
- GOAL-DIRECTED DESIGN METHODOLOGIES: A PROCESS OVERVIEW, TYPES OF USERS
- USER RESEARCH: TYPES OF QUALITATIVE RESEARCH, ETHNOGRAPHIC INTERVIEWS
- USER-CENTERED APPROACH, ETHNOGRAPHY FRAMEWORK
- USER RESEARCH IN DEPTH
- USER MODELING: PERSONAS, GOALS, CONSTRUCTING PERSONAS
- REQUIREMENTS: NARRATIVE AS A DESIGN TOOL, ENVISIONING SOLUTIONS WITH PERSONA-BASED DESIGN
- FRAMEWORK AND REFINEMENTS: DEFINING THE INTERACTION FRAMEWORK, PROTOTYPING
- DESIGN SYNTHESIS: INTERACTION DESIGN PRINCIPLES, PATTERNS, IMPERATIVES
- BEHAVIOR & FORM: SOFTWARE POSTURE, POSTURES FOR THE DESKTOP
- POSTURES FOR THE WEB, WEB PORTALS, POSTURES FOR OTHER PLATFORMS, FLOW AND TRANSPARENCY, ORCHESTRATION
- BEHAVIOR & FORM: ELIMINATING EXCISE, NAVIGATION AND INFLECTION
- EVALUATION PARADIGMS AND TECHNIQUES
- DECIDE: A FRAMEWORK TO GUIDE EVALUATION
- EVALUATION
- EVALUATION: SCENE FROM A MALL, WEB NAVIGATION
- EVALUATION: TRY THE TRUNK TEST
- EVALUATION PART VI
- THE RELATIONSHIP BETWEEN EVALUATION AND USABILITY
- BEHAVIOR & FORM: UNDERSTANDING UNDO, TYPES AND VARIANTS, INCREMENTAL AND PROCEDURAL ACTIONS
- UNIFIED DOCUMENT MANAGEMENT, CREATING A MILESTONE COPY OF THE DOCUMENT
- DESIGNING LOOK AND FEEL, PRINCIPLES OF VISUAL INTERFACE DESIGN
- PRINCIPLES OF VISUAL INFORMATION DESIGN, USE OF TEXT AND COLOR IN VISUAL INTERFACES
- OBSERVING USER: WHAT AND WHEN HOW TO OBSERVE, DATA COLLECTION
- ASKING USERS: INTERVIEWS, QUESTIONNAIRES, WALKTHROUGHS
- COMMUNICATING USERS: ELIMINATING ERRORS, POSITIVE FEEDBACK, NOTIFYING AND CONFIRMING
- INFORMATION RETRIEVAL: AUDIBLE FEEDBACK, OTHER COMMUNICATION WITH USERS, IMPROVING DATA RETRIEVAL
- EMERGING PARADIGMS, ACCESSIBILITY
- WEARABLE COMPUTING, TANGIBLE BITS, ATTENTIVE ENVIRONMENTS